Phishing attacks and other email compromise schemes are not just an annoyance in the modern workspace. A successful email compromise can allow malicious actors to intrude into an organization’s enterprise email accounts, expose sensitive data contained in users’ inboxes, and give cyber criminals the ability to successfully impersonate an employee to others within and without the organization by using the employee’s own email account.
Read more »Data Privacy & Cybersecurity
-
 Improving Your Office365 Security Posture to Stop Phishing at Email’s Shores Posted on: April 03, 2019 In: Data Privacy & Cybersecurity
Improving Your Office365 Security Posture to Stop Phishing at Email’s Shores Posted on: April 03, 2019 In: Data Privacy & Cybersecurity
-
 The Financial Fraud Kill Chain: Combatting Fraudulent Money Transfers Posted on: April 02, 2019 In: Data Privacy & Cybersecurity
The Financial Fraud Kill Chain: Combatting Fraudulent Money Transfers Posted on: April 02, 2019 In: Data Privacy & CybersecurityBusinesses are constantly targeted by criminals attempting to gain access to information that will allow them to fraudulently divert wire transfers. This often occurs after the criminal has conducted sufficient reconnaissance to determine who likely has an occupational role to approve or initiate wire transfers. The employee will then be targeted – often a financial executive like a Chief Financial Officer – and their email account will be compromised. But this can be prevented.
Read more »
-
 Emerging Trend: Managed Service Providers Targeted with Ransomware Posted on: March 25, 2019 In: Data Privacy & Cybersecurity
Emerging Trend: Managed Service Providers Targeted with Ransomware Posted on: March 25, 2019 In: Data Privacy & CybersecurityAn emerging cyber-attack trend is shifting the paradigm for both cyber-preparedness and incident response: ransomware attacks targeting managed service providers. This is, in part, because the size of these attacks can be an order of magnitude larger in terms of the number of entities that are simultaneously affected, and because of the corresponding large-scale efforts that must be undertaken to swiftly and effectively remediate these attacks.
Read more »
-
 Choosing the Wrong Partners in a Ransomware Attack - Making a Bad Situation Worse Posted on: March 22, 2019 In: Data Privacy & Cybersecurity
Choosing the Wrong Partners in a Ransomware Attack - Making a Bad Situation Worse Posted on: March 22, 2019 In: Data Privacy & CybersecurityCompanies who make a Bitcoin payment in the face of a ransomware attack may run afoul of U.S. anti-money laundering laws. In particular, any company that makes such a payment risks being categorized as a “money service business” under the Bank Secrecy Act and corresponding U.S. Treasury regulations, opening them up to a whole host of compliance statutes and regulations.
Read more »
-
 Illinois Expands the Definition of “Injury” Under the Biometric Information Privacy Act Posted on: March 01, 2019 In: Data Privacy & Cybersecurity
Illinois Expands the Definition of “Injury” Under the Biometric Information Privacy Act Posted on: March 01, 2019 In: Data Privacy & CybersecurityA recent decision issued by the Supreme Court of Illinois seems to stand for the proposition that the risk of harm to an individual stemming from a violation of the Illinois Biometric Privacy Act is so great that an impacted individual need not establish actual harm or injury to bring a claim. Rather, according to the Supreme Court of Illinois, exposure to the risk of actual harm or injury, standing alone, is sufficient.
Read more »
-
 It’s a Bird, It’s a Plane, No… It’s Cryptojacking! Posted on: February 27, 2019 In: Data Privacy & Cybersecurity
It’s a Bird, It’s a Plane, No… It’s Cryptojacking! Posted on: February 27, 2019 In: Data Privacy & CybersecurityYou attempt to log on to your computer, but it is non-responsive. Other users are also having trouble logging on. The system becomes so slow that it is non-functional. Is it an encryption attack? Is there some sort of malware affecting the network that will result in some form of extortionate demand? Or is it something else? Could it be that someone has “cryptojacked” the network?
Read more »
-
 HIPAA Breach Reporting: Focus on Remediation in Responding to an HHS/OCR Investigation Posted on: February 25, 2019 In: Data Privacy & Cybersecurity
HIPAA Breach Reporting: Focus on Remediation in Responding to an HHS/OCR Investigation Posted on: February 25, 2019 In: Data Privacy & CybersecurityLast year was another banner year for HIPAA data breaches reported to the Department of Human Services Office of Civil Rights (HHS/OCR), and the reporting period hasn’t yet closed, as organizations experiencing breaches affecting fewer than 500 individuals have until 60 days after the end of the calendar year in which the breach occurred to make the report.
Read more »
-
 Cybersecurity: Who Can Certify Compliance to the NYDFS Posted on: January 30, 2019 In: Data Privacy & Cybersecurity
Cybersecurity: Who Can Certify Compliance to the NYDFS Posted on: January 30, 2019 In: Data Privacy & CybersecurityThe New York State Department of Financial Services (NYDFS) Cyber Security Regulation for Financial Services Companies 23 NYCRR 500, enacted in March 2017 (the “Regulation”), sets out the required framework for regulated entities’ information security programs. The NYDFS Cybersecurity Regulation applies to “Covered Entities,” which are organizations required to operate under NYDFS...
Read more »
-
 Massachusetts Amends Data Breach Law Notice Requirements, Mandates Credit Monitoring Services Posted on: January 24, 2019 In: Data Privacy & Cybersecurity
Massachusetts Amends Data Breach Law Notice Requirements, Mandates Credit Monitoring Services Posted on: January 24, 2019 In: Data Privacy & CybersecurityMassachusetts recently updated its breach notification statute, requiring an organization to provide additional services for individuals and greater disclosures to state regulators when a data breach occurs. The changes go into effect on April 10, 2019
Read more »
-
 Modlishka – Exploiting Two-Factor Authentication Posted on: January 22, 2019 In: Data Privacy & Cybersecurity
Modlishka – Exploiting Two-Factor Authentication Posted on: January 22, 2019 In: Data Privacy & CybersecurityTwo-factor authentication (2FA) is a commonly used means of securing access to website accounts through easily understood login procedures. Once the user provides the required information, whether a password or site generated code, a session cookie is generated and a secure session is established between the user and the site. But what if an unauthorized person eavesdrops and collects the 2FA information or session cookie?
Read more »
-
 Identity Theft: The Crime of the New Millennium - Tips for Prevention and Recovery Posted on: January 17, 2019 In: Data Privacy & Cybersecurity
Identity Theft: The Crime of the New Millennium - Tips for Prevention and Recovery Posted on: January 17, 2019 In: Data Privacy & CybersecurityTwenty years ago, as I was working with the FBI and the Secret Service in prosecuting large identity theft rings – often associated with data breaches (although the term “data breach” had not yet entered our daily vernacular) – we created protocols to help consumers prevent identity theft and assist victims recovering from it.
Read more »
-
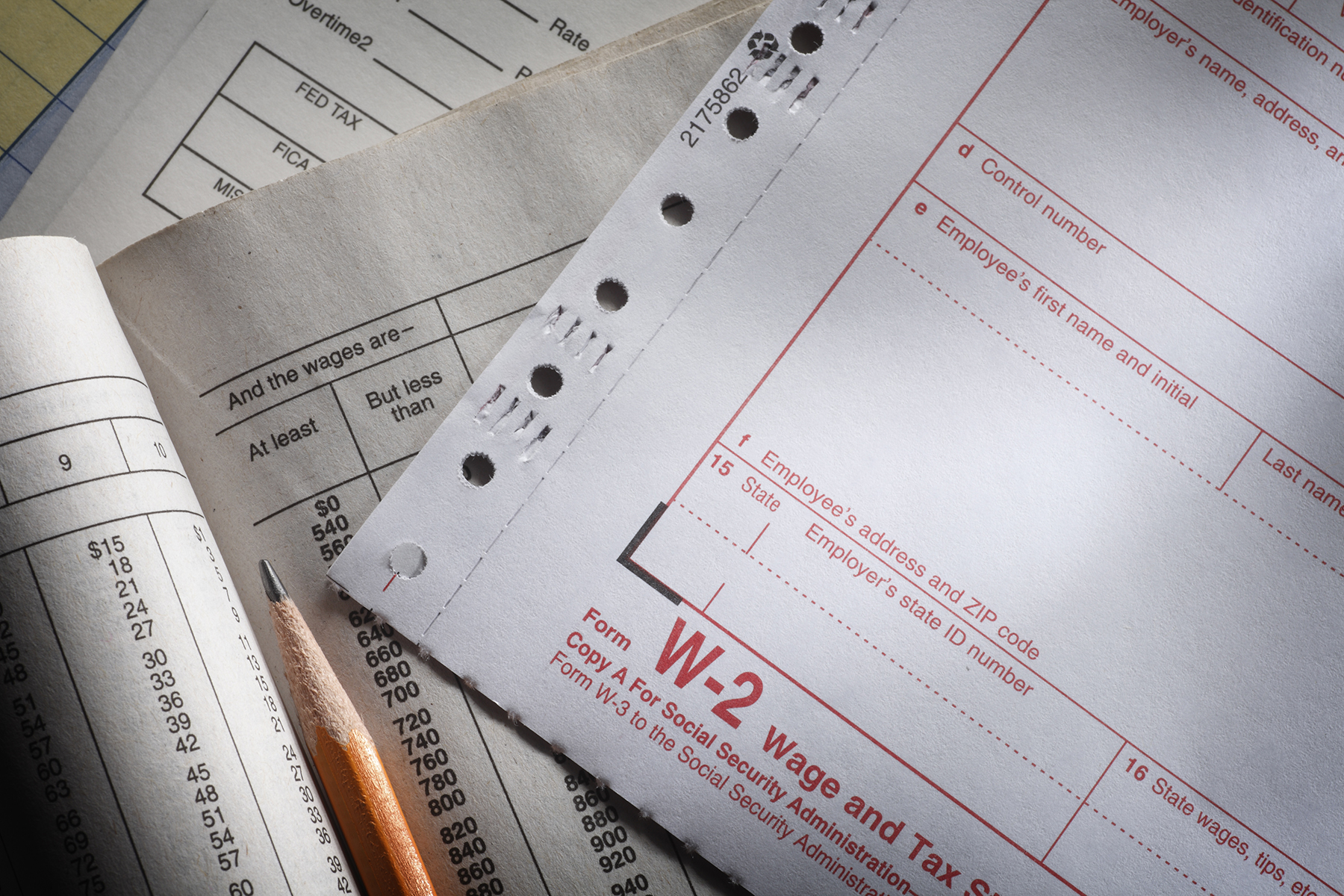 W-2 Image Exploits: With the Tax Season Come the Thieves Posted on: January 10, 2019 In: Data Privacy & Cybersecurity
W-2 Image Exploits: With the Tax Season Come the Thieves Posted on: January 10, 2019 In: Data Privacy & CybersecurityIf you process or store Form W-2 Wage and Tax Statements, you are a target. The Form W-2 contains everything a malicious actor needs to file a false tax return with the Internal Revenue Service (IRS) and steal a refund. Because a W-2 contains a consumer Social Security number (SSN), it is highly valued on the dark web, and therefore highly sought after by thieves.
Read more »
 Data Privacy & Cybersecurity Practice
Data Privacy & Cybersecurity Practice