NY Cyber Regs Compliance Deadline Looms for Financial Firms
Posted on: August 10, 2017
Tags:
new york, department of financial services, financial firms, incidence response plan, cyber threatIn: Data Privacy & Cybersecurity
August 28, 2017, marks the end of the initial 180-day transition period for covered entities to come into compliance with New York’s new financial cybersecurity regulations.
By: Lewis Brisbois' Data Privacy & Cybersecurity Team

Protecting sensitive customer and business information from data thieves is nothing new for the financial industry. But come August 28, 2017, banking, insurance, and other financial services companies in the Empire State must implement specific cyber protections and policies to be in compliance with cybersecurity regulations promulgated earlier this year.
On March 1, 2017, new cybersecurity regulations issued by the New York Department of Financial Services (DFS) (23 NYCRR 500) went into effect, requiring banks, insurers, and other financial services institutions licensed in New York to implement measures to protect the integrity of their systems and sensitive information. The new DFS regulations also make financial services firms’ officers and boards of directors responsible for approving company cyber policies and annually certifying their compliance with the new regulations.
But financial service companies are not the only entities affected by the new regulations. Indeed, third-party service providers — including law firms, accounting firms, and other professions that regularly access sensitive, nonpublic information held by a regulated financial services company as part of their services — also have to meet certain cybersecurity benchmarks.
Financial services firms regulated by the state of New York were given an initial 180-day transition period to review and augment their cybersecurity policies and programs to come into compliance with the majority of the new regulations’ provisions. The Empire State has set staggered deadlines — March 1, 2018, September 3, 2018, and March 1, 2019, respectively — to implement the remainder of the required cybersecurity policies, procedures, and measures.
Security controls cannot mitigate all the risk from current online threats, however. Firms subject to New York’s cyber regulations should also review their insurance coverages to mitigate the economic risk posed by the evolving digital threats. In our ever-evolving digital environment, insufficient insurance coverage can result in catastrophic economic consequences.
New Duties for Financial Firms
Under DFS’ new regulations, a company operating under New York’s banking, insurance, or financial services laws (“covered entity”) must take a number of measures to protect the information systems and the nonpublic information it holds. This includes personally identifiable information or health information related to an individual, as well as critical business information where the disclosure would adversely impact the covered entity.
For instance, a covered financial services company must create a cybersecurity program designed to protect the confidentiality, integrity, and availability of its information systems. The cybersecurity program must be based on the company’s risk assessment and must:
- Identify cybersecurity risks to nonpublic information stored on the covered entity’s information systems;
- Protect the covered entity’s information systems and any nonpublic information from unauthorized access, use, or other malicious acts;
- Detect, respond to, and mitigate any negative effects from a “cyber event” — that is, any attempt to gain unauthorized access to or disrupt the covered entity’s system or information stored therein;
- Recover from and return to normal operations after a cyber event; and
- Fulfill the covered entity’s regulatory reporting obligations.
As part of the cybersecurity program, a covered entity must also develop a written incident response plan, and must create a cybersecurity policy addressing information security, customer data privacy, incident response, and a host of other cyber-related issues. Moreover, a covered entity must implement minimum cybersecurity standards established by the new regulations, including but not limited to:
- Performing periodic risk assessments;
- Conducting periodic penetration tests and bi-annual vulnerability assessments of identified risks;
- Imposing restrictions on nonpublic information access privileges;
- Establishing an audit trail to reconstruct “material financial transactions” and maintain such records for at least five years;
- Encrypting nonpublic information both in transit and at rest or protecting by other controls; and
- Utilizing multi-factor authentication.
Other important requirements include:
- Designating a chief information security officer;
- Employing cybersecurity personnel to manage the cybersecurity program;
- Implementing third-party provider security policies and requiring vendors to follow minimum cybersecurity practices;
- Conducting cybersecurity training for employees;
- Notifying the DFS Superintendent within 72 hours after discovery of a cyber event; and
- Annually certifying the covered entity’s compliance with the regulations.
Officers Must Now Certify and Sign Off on Cyber Policies and Practices
The DFS’ new regulations also now make cybersecurity a C-Suite responsibility. A covered entity’s board of directors or designated senior officer(s) must approve its cybersecurity policies and sign off on the entity’s annual compliance certification to DFS starting in 2018.
The overall effect of these duties is to ensure that a covered entity’s senior leadership is aware of — and ultimately responsible for — its cybersecurity practices, policies, and vulnerabilities. Yet this may ultimately open a covered entity’s officers or board up to new legal and regulatory liabilities, even if the firm does not suffer a data breach. As an example, a covered entity may be subject to a DFS investigation if a senior officer certifies the existence of a cybersecurity policy that does not accurately reflect the entity’s actual practices or policies.
Additionally, an inaccurate representation of the existence a cybersecurity policy approved by a covered entity’s higher echelon officer, or a failure to meet the cybersecurity standards outlined in New York’s rules, could expose the firm, its board, and its officers to greater liability following a breach. In the end, any financial firm covered by the new regulations should examine the downstream liabilities that may result if they do not meet their new cybersecurity duties.
Third-Party Service Providers Must Also Meet Cyber Standards
The cyber practices of financial service companies’ third-party service providers are also affected by the new rules. As part of its own policies and procedures, a covered entity now must have a “Third-Party Service Provider Security Policy” — i.e., relevant due diligence guidelines or contractual provisions to ensure its third-party service providers have sufficient cybersecurity measures in place. Such measures include, where applicable:
- Controlling and limiting access to sensitive information — including the use of multi-factor authentication;
- The use of encryption to protect nonpublic information in transit and at rest; and
- Appropriate consumer and regulatory notification processes in the event of a cyber event.
Moreover, the covered entity’s policies must detail representations and warranties requirements from third-party service providers as to their cyber policies and procedures.
In addition, a covered entity must now conduct oversight of their third-party service providers’ cybersecurity programs. Importantly, a covered entity must address in its policies and procedures the minimum cybersecurity practices it requires of its third-party service providers, as well as the due diligence processes the covered entity uses to evaluate whether its providers’ cyber practices are adequate. Finally, a covered entity has to periodically assess the risks presented by, and the continued adequacy of, its providers’ practices.
A third-party vendor’s own cybersecurity is a crucial link in a company’s overall cyber defenses, to be sure. As recent history has shown, the cyber vulnerabilities of an outside vendor can have disastrous consequences for the company that hired them, even if it did not suffer a direct cyber event itself. And vendors who routinely have access to their clients’ sensitive information are increasingly targets of cybercriminals seeking backdoor access to a company’s confidential data. Law firms and similar vendors are especially sensitive targets, as they typically contain data on not one, but hundreds — or even thousands — of clients whose information could be exploited by data thieves. Indeed, the U.S. Department of Justice indicted three foreign nationals in 2016, accusing the defendants of hacking into law firms to steal and exploit their clients’ sensitive and confidential information.
But all of these duties — upon both the third-party service providers and the covered entities themselves — impose substantial burdens on any provider that works for a financial institution regulated by the Empire State. First, third-party providers now must take a hard look at their cybersecurity practices and policies to ensure that they are in line with the DFS’ rules. Second, covered entities must be involved in their third-party providers’ cyber practices by setting standards for their providers to meet. Thus, third-party providers should expect covered entities to routinely scrutinize their cybersecurity measures and policies. Finally, third-party providers may be exposed to greater legal liabilities following a cyber event if they are not fully in line with their duties under New York’s cyber regulations.
Key Compliance Target Dates for Financial Services Companies
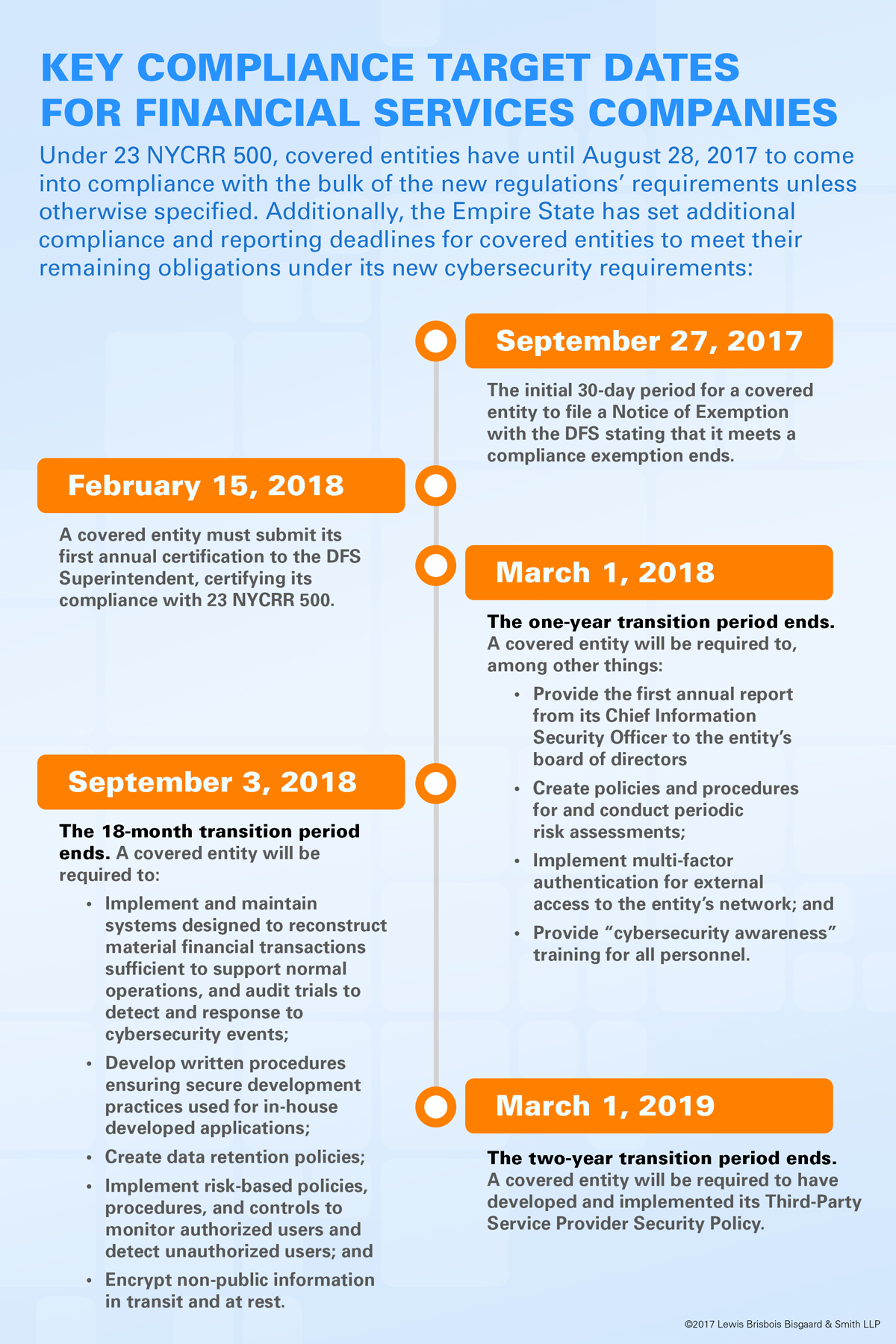
Under 23 NYCRR 500, covered entities have until August 28, 2017, to come into compliance with the bulk of the new regulations’ requirements unless as specified otherwise below. Furthermore, the Empire State has set additional compliance and reporting deadlines for covered entities to meet their remaining obligations under its new cybersecurity requirements:
- September 27, 2017: The initial 30-day period for a covered entity to file a Notice of Exemption with the DFS stating that it meets a compliance exemption ends.
- February 15, 2018: A covered entity must submit its first annual certification to the DFS Superintendent, certifying its compliance with 23 NYCRR 500.
- March 1, 2018: The one-year transition period ends. A covered entity will be required to, among other things:
- Provide the first annual report from its chief information security officer to the entity’s board of directors
- Create policies and procedures for and conduct periodic risk assessments;
- Implement multi-factor authentication for external access to the entity’s network; and
- Provide “cybersecurity awareness” training for all personnel.
- September 3, 2018: The 18-month transition period ends. A covered entity will be required to:
- Implement and maintain systems designed to reconstruct material financial transactions sufficient to support normal operations, and audit trials to detect and response to cybersecurity events;
- Develop written procedures ensuring secure development practices used for in-house developed applications;
- Create data retention policies;
- Implement risk-based policies, procedures, and controls to monitor authorized users and detect unauthorized users; and
- Encrypt non-public information in transit and at rest.
- March 1, 2019: The two-year transition period ends. A covered entity will be required to have developed and implemented its Third-Party Service Provider Security Policy.
Review Practices and Coverage in Light of New Cyber Responsibilities
Whether a covered entity or third-party provider, a firm encompassed by DFS’ cyber rules may be asking, “What do we do now?” First and foremost, financial services firms and their vendors should review their current cyber policies and security measures to ensure that they are in line with the new rules and sufficient to meet their particular cybersecurity risk tolerances. Companies should weigh whether their cyber policies meet current security standards and best practices, ensure that periodic risk assessments are conducted, and develop or revise their incident response plan to ensure they can effectively respond to a cyber event.
Such companies should also engage outside counsel well-versed in cybersecurity issues and liabilities to assess their compliance with the New York cybersecurity rules, as well as standards set forth by the Federal Trade Commission and other data security and privacy regulators.
Second, businesses affected by these rules should bear in mind that claims which may arise out of or relate to New York’s cyber rules may not be covered by traditional commercial general liability policies, as such policies generally exclude cyber-related claims and losses from coverage.
Third, covered firms should examine their Directors’ and Officers’ policies carefully to ensure that their D&O coverages include possible liabilities that may result from directors and officers attesting to their companies’ cyber practices.
Finally, financial services firms should ensure that their current cyber insurance policies are robust enough to cover their potential liabilities. Technology can mitigate only so much risk associated with current online threats. The remaining risk should be transferred to cyber insurance, and acquiring sufficient coverage should be a priority.

